
We place locks on our doors for security in the first place. We then add smart locks to add convenience to our lives. How much is that convenience worth though? Can we add smart lock technology without compromising securitt? Here are the best options to achieve just that.
What Is The Most Secure Smart Lock? My recommendation for the most secure smart lock for residential customers is the Nest × Yale Smart Lock. The Nest × Yale Smart Lock offers AES-128 encrpytion, a keyless lock to prevent physical attacks, and offers the capability to use two-factor authentication.
On top of the physical security requirements of traditional door locks, smart locks need an additional level of security to protect the data that is electronically transmitted in the home network, as well as over the internet. Here is a detailed look at the security of locks.
How is Security Traditionally Measured For a Lock?
They rank security in terms of physical resistance to given attacks: bumping, kicking in, etc
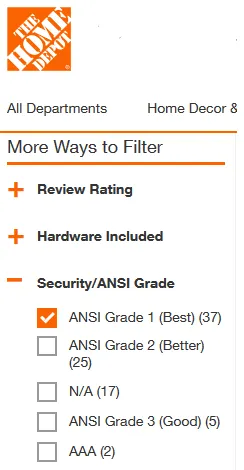
Even without adding in the complications of a smart lock, selecting the right lock to place on your front door can be a bit perplexing. There are two main standards that can be looked at two determine the overall security of a deadbolt lock:
- ANSI/BHMA Grade
- UL 427 Listing
ANSI/BHMA Grade
ANSI is a not-for-profit organization dedicated to supporting the U.S. voluntary standards and conformity assessment system and strengthening its impact both domestically and internationally.
ANSI Brochure
Standards are what help to create best practices. As an example, if a part or device meets a certain building standard, when the building inspector comes to inspect the house, they will know that particular device meets building code because it was designed and meets a certain standard.
The Builders Hardware Manufacturers Association (BHMA®) is the only organization accredited by the America National Standards Institute (ANSI) to develop and maintain performance standards for locks…
Buiders Hardware
The particular standard we are interested in for locks is ANSI/BHMA A156.2-2017 – American National Standard for Bored & Preassembled Locks and Latches
A brief description of the highlights can be found on their website here, as well as what I describe below. Payment is required for full copies of the standard.
The standard has three main categories: Durability, Safety & Security, and Appearance. Each category is ranked from 1 (the highest grade) to 3 (the lowest grade).
Durability: The locks are tested to withstand a certain level of opening and closing cycles.
Safety & Security: The locks are tested to withstand a certain amount of force.
Appearance: According to BHMA, resistance to corrosion, chemicals, abrasion, and sunlight are all considered in an array of finish tests.
| Grade 1 | Grade 2 | Grade 3 | |
| Durability | Can withstand 1 million opening and closing cycles. | Can withstand 800,000 opening and closing cycles. | Can withstand 800,000 opening and closing cycles. |
| Security | 1 Inch Latch Bolt Can withstand 10 strikes of 75 pounds of force. | 5/8 Inch Latch Bolt. Can withstand 5 strikes of 75 pounds of force. | 5/8 Inch Latch Bolt. Can withstand 2 strikes of 75 pounds of force. |
| Appearance | All grades must meet the same requirements. | All grades must meet the same requirements. | All grades must meet the same requirements. |
The grading conditions are described in slightly more detail on the ANSI blog page located here.
Grade 1 locks are typically used for businesses or other commercial applications, where more security is needed.
Grade 2 locks are typically used for residential purposes on exterior facing doors, such as your front door.
Grade 3 locks are designed to be a secondary security measure, meaning they would have to get through your primary security first (such as your front door). These are locks that you might find on a closet door inside the house.
UL 427 Listing
“UL” is short for Underwriters Laboratories. They are another company that produces standards and they are seen as a global safety certification company. Many products we use are UL listed, just check an extension cord and you will find a UL tag (Hopefully!)
The UL 437 deadbolt security test is one of the hardest to pass. It tests a lock against impressioning, forcing, drilling, sawing, prying, picking and bumping. Along with the lock-pick test, the UL 437 also tests for: Field changeable keys, tight-fitting bolts, and ability to withstand 10,000 opening and closing cycles.
UL 437 locks are typically referenced as high-security locks. They are used in situations where a person needs confidence that the lock will not be compromised. These locks are not typically used in residential applications. However, here is a video of one brand that targets residential uses that demonstrates the locks effectiveness.
Keep in mind, a lock is only as good as the door that it is installed on. If you have a cheap wood door and a high-security lock, chances are, a thief will just kick the door in. Get a good door and reinforced frame to match the hardware if you really want protection.
Traditional Lock Security Challenges
Don’t be lulled into a false sense of security just because you have a traditional lock instead of a smart lock. Most locks on residential housing aren’t that great. You can get a lock picking kit from Amazon that will pick most every residential lock in a matter of minutes for just a few bucks. Learning to pick locks is something you can become pretty good at (or good enough at) in just a few hours of trial and error.
Secondly, how many of you have, or have ever, had a spare key hidden somewhere outside of the house? That is a very common thing to do and completely neglects placing a lock on the house. In the case of a smart lock, there is no need to re-key or buy new locks because a key has been lost or stolen.
Related: Why Use Smart Locks? The 10 Benefits You Need to Know
How is Security Measured For a Smart Lock?
This is where things get a little tricky.
Locks have been around a really, really long time. Some research suggests that locks have been around for over 6000 years, when they were created by the ancient Egyptians. The standards the measure the security of a lock have been around a long time as well, although not quiet that long. The first edition of UL 437 was created in 1953
Internet connected locks produced for consumer use have only existed for a few years. Standards for defining how electronically secure a smart lock is have yet to be defined. The mechanical standards mentioned for traditional locks (ANSI/BHMA A156.2 & UL 437) can still be applied to smart locks.
IoT Security
How do we measure security of a smart lock if a standard hasn’t been defined? We take a step up and look at the bigger picture of cybersecurity and IOT security.
The Internet of things (IoT) is a system of interrelated computing devices, mechanical and digital machines provided with unique identifiers (UIDs) and the ability to transfer data over a network without requiring human-to-human or human-to-computer interaction.
Wikipedia
Any smart home device that is connected to the internet, either directly or indirectly, falls into this category. In other words, if you can control a device remotely, even through a hub, it is part of the Internet of Things.
IoT security is the practice of protecting those devices against cybercrime. IoT falls under the realm of cyber-security, which is hopefully a topic we have all at least heard of. It’s an area of ever-growing concern and scruitiny, after high-profile attacks continue to happen year after year.
Remember the Target breach back in 2013? The hackers accessed secure elements of Target’s network through a HVAC system that was connected to the internet. The hackers then installed malware onto Target’s network.
IoT Security Measures
It’s inevitable that systems are going to be hacked, but there are ways to help prevent that from happening that can be designed into the devices hardware and software. TechTarget has compiled a great list describing these measures. Their article on the topic can be seen here, and is highlighted in the seven topics below.
Incorporating security at the design phase. IoT developers should include security at the start of any consumer-, enterprise- or industrial-based device development. Enabling security by default is critical, as well as providing the most recent operating systems and using secure hardware.
Hardcoded credentials should never be part of the design process. An additional measure developers can take is to require credentials be updated by a user before the device functions. If a device comes with default credentials, users should update them using a strong password or multifactor authentication or biometrics where possible.
PKI and digital certificates. Public key infrastructure (PKI) and 509 digital certificates play critical roles in the development of secure IoT devices, providing the trust and control needed to distribute and identify public encryption keys, secure data exchanges over networks and verify identity.
API security. Application performance indicator (API) security is essential to protect the integrity of data being sent from IoT devices to back-end systems and ensure only authorized devices, developers and apps communicate with APIs.
Identity management. Providing each device with a unique identifier is critical to understanding what the device is, how it behaves, the other devices it interacts with and the proper security measures that should be taken for that device.
Hardware security. Endpoint hardening includes making devices tamper-proof or tamper-evident. This is especially important when devices will be used in harsh environments or where they will not be monitored physically.
Strong encryption is critical to securing communication between devices. Data at rest and in transit should be secured using cryptographic algorithms. This includes the use of key life-cycle management.
Smart Lock Security Challenges
The primary issue of having a smart lock, or any other device in your house connected to the internet is that it is accessible to hackers. Identifying smart locks with the security prevention mechanisms described above can help protect your smart lock.
Hackers are unauthorized users who break into systems. The reasons are varied, from just having fun all the way to malicious intent including stealing money or identity. Hacker after hacker have exposed critical security flaws in some of the most high-profile smart locks on the market.
Here is one example of a popular smart lock brand that was hacked. These issues have since been fixed, ut that doesn’t mean there aren’t other ways the lock can be hacked.
That was an example of a name-brand smart lock being attacked and hacked. It was somewhat complex and was dones by someone with extensive computer knowledge. However, a lot of off-brand smart locks are simmple to hack and often use plain-text passwords. A big No-No in the security world.
Another concerning method is accessing your smart lock through other devices on the network that can control the lock, for example, your smart hub. Here is an article from a group known as Blackmarble describing how that was accomplished.
Most Secure Smart Lock
Knowing what we know now, here is my recommendation for smart lock based on its designed built-in security features.
I recommend the Nest × Yale Smart Lock. I recommend this smart lock because of the following features that are answered on Google’s website here.
- The Nest × Yale Lock is designed to be secure and durable. It is certified to ANSI/BHMA (A156.36, Grade 2).
- Nest × Yale Lock is key-free. Keyed locks can be easily picked or bumped. This lock does not provide that option.
- The Nest × Yale Lock is able to detect tampering. It will send a notification to your phone and sound the built in alarm when tampered with.
- The Nest × Yale Lock uses AES 128-bit encryption whenever it’s communicating with other devices in your home or the outside world.
- Encrypted passcodes are stored directly on the lock. This greatly reduces the chance of your passcode being intercepted or stolen.
- The Nest × Yale Lock uses Bluetooth, but only when you’re installing and setting it up. It doesn’t use Bluetooth for day-to-day functions. You won’t be able to unlock your door or change any settings over Bluetooth.
- Option to use Two-Factor Authentication.
Runner Up
The runner up to the Nest x Yale is the August Wi-Fi Smart Lock. Yale and August are both owned by the same parent company, Assa Abloy.
The August lock still has a keyed entry, which leaves open the vulnerabilities of a traditional lock. August lists the following security features on their website (which can be seen here).
Encryption
August Smart Lock uses both Bluetooth Energy (BLE) technology encryption and TLS in our mobile applications.
Authentication
August products offer an added level of security by requiring users to verify their identity with a second form, either an email or phone number.
Lost Phone
Quickly and easily disable your August app and all virtual keys at any time on any of your associated devices at: lostphone.august.com
How You Can Increase Your Smart Lock Security
1. Re-name your router
The default name the manufacturer gave the router might identify the make or model, allowing hackers to exploit known vulnerabilities. Give your router an unique name that is not tied to your name or your street address. This will help your router name from giving away any personal identifiers.
2. Use strong encryption method for Wi-Fi access
In your router’s settings, you want to use a strong encryption method, like WPA2, when setting up access to your Wi-Fi network. This type of encryption is typically the default for most modern routers, but it doesn’t hurt to check. This will help keep your network and communications secure, and unwanted people off your network.
3. Use a guest network
Keep your main Wi-Fi network to yourself and private. Guest Wi-Fi networks help to protect the primary network from security threats such as network worms or malware that could otherwise spread to other smart devices on the same network. Visitors, friends and relatives can log into the guest network, which doesn’t tie into your IoT devices.
4. Change default login credentials
Default passwords the come with routers and smart devices and common knowledge and can be found easily with a Google search. Many people, including cybercriminals, have already memorized the default passwords that come with many IoT products because they use them so much. That makes it easy for them to access your IoT devices and any accessible information on them once logged in. If you are considering a device that doesn’t allow changing the default password, please consider a different one. That should be a big red flag.
5. Use strong, unique passwords for your accounts
Avoid common words or passwords that are easy to guess, such as “password” or “123456.” Instead, use unique, complex passwords made up of letters, numbers, and symbols. You might also consider a password manager, which can store complex, hard-to-memorize passwords.
6. Check default settings for your devices
In addition to default logins, your IoT devices might come with default privacy and security settings. Browse through them and change them as necessary, as some default settings could benefit the manufacturer more than they benefit you.
7. Disable features you do not need
IoT devices come with a variety of services and features, such as remote access. These features are often enabled by default to make the user experience more smooth. However, if you don’t need it, be sure to disable it when possible.
8. Keep your software updated
When your smart phone manufacturer sends you a software update, don’t put off installing it. It might be a patch for a security flaw. I now they get released monthly, or more often, and can be annoying, but gettign hacked is more annoying. Security of your smart phone is important, since you may connect to your smart home through it.
The manufacturers of your smart devices will also send out updates. Be sure to download updates and apply them to your device to help stay safe. When possible, just make updating automatic so you won’t have to deal with the hassle of updating software everyday.
9. Audit your current IoT devices
This is a good activity to do once a year or so. Devices already on your home network can become outdated. For example, it could be time to upgrade that old security camera. Take time to check if newer models might offer stronger security as well as features that could be of benefit to you.
10. Use two-step authentication
Two-factor authentication, such as a one-time code sent to your phone or email, can keep the bad guys out of your accounts. If your smart-device apps offer two-factor authentication, often abbreviated 2FA, use it!
If you receive a text or email with a code, but did not request it, that means someone is trying to hack into your account and they have your correct password. Go change your password ASAP, as well as any other accounts that use that password.
11. Avoid public Wi-Fi networks
If your out and about, you might want to manage your smart devices through your smart phone in a coffee shop or somewhere with free Wi-Fi in order to help save data on your data plan. STOP! Don’t do it! If you must be on public Wi-Fi, which is generally not a good idea, use a VPN to encrpyt your data. Traffic on a public network can be seen by everybody on that network. Hackers will often use this method.
In Conclusion
More and more IoT devices are coming, and they will angle for a place in your home. If they make your life more convenient, great. But don’t forget to secure your increasingly smart home and your IoT devices. Do your research before buying, and your due diligence after purchase by setting up security features.
